Blog

WordPress Plugin Vulnerabilities: 7,966 Reasons to Pay Attention
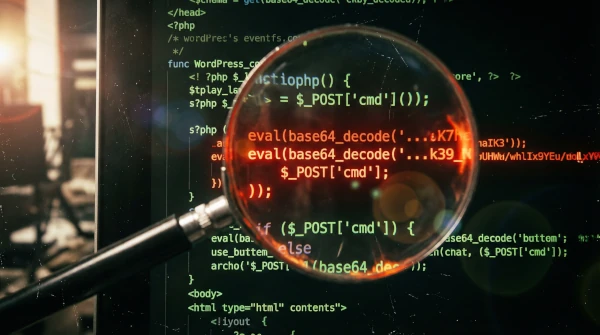
You installed a plugin to add a contact form.Another one for SEO.One more for that slider your designer insisted on in 2019.A caching plugin.A security plugin.A plugin to manage your other plugins. Sound familiar? Welcome to WordPress, where the average site runs 20+ plugins and every single one is a potential open window into your business. 7,966 Is Not a Typo That’s the number of new plugin vulnerabilities recorded in 2024 alone.Not total.Not since WordPress started.In one year. That’s roughly 22 new ways to break into a WordPress site discovered every single day. And here’s the part that should ruin your lunch:96% of all WordPress vulnerabilities come from plugins. Not WordPress itself.Not your theme.The things you installed to make your site better are the things making it vulnerable. It’s like putting five new locks on your front door while leaving every window wide open. “But I Keep My Plugins Updated”

Why Hackers Love Small Business Websites
It is only logical to assume hackers go after the big fish — banks, tech companies, government agencies.And sure, those make the news.But here’s the uncomfortable truth: Hackers absolutely love your website. Not because you’re important.Because you’re easy. It’s Not Personal. It’s Automated. Nobody is sitting in a dark room targeting your bakery’s WordPress site.That’s not how it works. Hackers use bots — automated scripts that scan every website on the internet, looking for known vulnerabilities. They don’t care if you sell cupcakes or consulting.They care if your plugins are outdated.And if they are? The bot walks right in. 30,000 WordPress sites get hacked every single day.Not because they were targeted.Because they were next on the list. The “I’m Too Small to Hack” Myth This is the most expensive belief in small business. 83% of small business owners think their site is either secure or not worth attacking. Meanwhile, the

What Hackers Actually Do With Your Small Business Website (It’s Not What You Think)
Most small business owners imagine a hack looks like this: a hacker breaks in, steals their customer data, and disappears. That’s the Hollywood version. The reality is both more mundane and more damaging — because what actually happens is usually invisible, ongoing, and specifically designed so you never notice. Here’s what hackers actually do when they compromise a small WordPress site. They turn your site into a spam cannon The most common use of a compromised small business site has nothing to do with your data. Attackers use your server to send thousands — sometimes millions — of spam and phishing emails. Why your server? Because your domain has an established reputation. Emails sent from a trusted domain bypass spam filters far more reliably than emails sent from a new, unknown server. Your domain becomes a tool for other attacks. You don’t notice, because the spam doesn’t go to your

The 7 Plugins Most Likely to Get Your Site Hacked in 2026
In 2025, 11,334 vulnerabilities were discovered in the WordPress ecosystem. 91% of them were in plugins — not WordPress core. The platform isn’t the problem. What you’ve installed on top of it is. Some plugin categories are consistently more dangerous than others — not because they’re poorly built, but because they’re complex, widely installed, and high-value targets. Here are the seven categories with the highest attack frequency in 2026, with real examples from the vulnerability database. 1. Page builders and their add-on pluginsPage builders are installed on tens of millions of sites, which makes them the most profitable target for attackers. The core builders themselves are relatively well-maintained — it’s the third-party add-on plugins where the danger concentrates. Plugins like King Addons for Elementor, Master Addons for Elementor, and The Plus Addons for Elementor have each appeared in multiple 2025–2026 vulnerability reports. A cross-site scripting or privilege escalation flaw in
Your WordPress Site Was Probably Attacked This Week. Here’s How to Check
You didn’t get an alert. Your site looks fine. Pages load, checkout works, contact form submits. So nothing happened, right? Not necessarily. Most WordPress compromises are silent by design. Attackers don’t deface your homepage — that would alert you immediately. Instead, they inject hidden spam links into your pages, redirect mobile visitors to phishing sites, or use your server to send thousands of emails — all while your site appears completely normal to you. Here’s how to check whether your site has already been compromised, without installing anything or hiring anyone. Step 1: Run a Google transparency checkGo to Google’s Safe Browsing tool and enter your URL. If Google has flagged your site for malware or phishing, it will show here. This is also what triggers the “This site may harm your computer” warning in search results. Step 2: Check your Google Search ConsoleLog into Search Console and look under